Diving into the world of cybersecurity often leads to one question: "Can I hire a hacker?". The response is a resounding yes, but with a essential caveat - understanding the difference between ethical and black hat hackers. Ethical consultants operate within legal boundaries, assisting organizations strengthen their infrastructure. They conduct ethical hacking to reveal weaknesses before malicious actors can exploit them. Conversely, black hat hackers are the antagonists, using their skills for malicious purposes like data breach. Engaging a black hat hacker is not only ethically wrong but also criminal and can lead to severe repercussions.
- Consequently, always choose an ethical hacker who adheres to a strict code of conduct and is transparent about their methods.
- Background checks are essential when identifying a hacker for hire.
Top Platforms to Recruit Cybersecurity Professionals
Securing the digital realm requires a skilled and dedicated workforce. Recruiting cybersecurity professionals is paramount for firms of all sizes, and navigating the talent landscape can be complex. Fortunately, several platforms have emerged as go-to resources for connecting with top experts in this field.
Here's a look at some of the top-rated platforms:
- LinkedIn: The undisputed giant in professional networking, Glassdoor boasts a vast pool of cybersecurity experts. Utilize its powerful search features to pinpoint candidates with the specific skills and experience you need.
- Cyberseek: These platforms specialize in connecting employers with tech talent, including cybersecurity specialists. They often feature niche listings for cybersecurity roles and offer insights into market trends.
- Codewars: For those seeking highly skilled developers and security analysts, these platforms provide a glimpse into the problem-solving prowess of potential candidates. They host challenges where individuals showcase their cybersecurity expertise.
By leveraging these platforms effectively, organizations can accelerate their cybersecurity recruitment Hacker einstellen professionellen process and attract top talent to protect their valuable assets.
Hiring Hackers Legally
In today's digital landscape, digital risks are more prevalent than ever. To stay ahead of the curve, businesses need to mitigate their systems and data. A vital strategy in this endeavor is employing ethical hackers, also known as penetration testers or cybersecurity experts. These skilled professionals can identify weaknesses in your systems before malicious actors leverage them.
Hiring ethical hackers legally requires a clear understanding of the regulatory landscape and best practices. Businesses need to establish comprehensive recruitment strategies that ensure compliance. This includes conducting thorough background checks, confirming expertise, and drafting legally binding agreements.
Additionally, businesses should build a culture of transparency when it comes to cybersecurity. This means promoting ethical hacking initiatives, providing training opportunities, and creating a safe space for employees to flag potential risks without fear of reprisal.
By following these guidelines, businesses can effectively leverage ethical hackers while ensuring legal compliance and mitigating cybersecurity risks.
Sourcing Top Security Experts
Landing the right proficient individuals is vital for any company. In the ever-evolving landscape of cybersecurity, finding top hackers has become more difficult than ever. To attract the best and brightest to your team, you need a targeted approach.
- Connect with authorities in the cybersecurity community. Attend conferences, engage with online forums, and build relationships with aspiring hackers.
- Showcase your work environment. Top talent are looking for more than just a paycheck. They want to be part of a supportive atmosphere where they can grow.
- Provide competitive compensation and perks. This is essential for securing top individuals in a fierce market.
- Offer opportunities for skill enhancement. Top security specialists are constantly advancing. Show them that you are committed to their development.
Remember that the best ethical coders are in high request. You need to showcase your value to attract them. Be creative in your methodology.
Ethical Hacking Jobs: Where to Find Skilled Talent Online online
Finding top-tier ethical hacking experts isn't always easy. That highly skilled practitioners are in high demand, making the search for qualified candidates a critical part of any successful cybersecurity team.
Luckily, the digital world offers a plethora of avenues to connect with talented ethical hackers. Here are just a few places to start your search:
* **Specialized Job Boards:** Websites like Hackers-Forum, Cyberseek, and Bugcrowd focus specifically on cybersecurity roles.
* **Social Media Networks:** Platforms like LinkedIn and Twitter are great for networking with ethical hackers and staying up-to-date on industry news.
* **Online Communities:** Forums and groups dedicated to ethical hacking provide a valuable space to interact with skilled experts.
Don't be afraid to get creative in your search! Attend cybersecurity events, participate in online challenges, and leverage your existing relationships to find the best ethical hacking talent.
Building Your Cybersecurity Team: Hiring Expert Hackers
In today's dynamic cybersecurity landscape, building a robust team of experts is paramount. However, finding the right talents can be a challenging task. That's where seeking expert hackers comes in. These individuals possess a unique skillset that allows them to anticipate and counter threats before they escalate.
- Utilizing their comprehensive knowledge of vulnerabilities, ethical hackers can proactively identify weaknesses in your systems and deploy safeguards to bolster your defenses.
- Additionally, expert hackers can conduct penetration assessments to mimic real-world attacks, revealing potential vulnerabilities that may have otherwise gone overlooked.
- In conclusion, incorporating expert hackers into your cybersecurity team can provide a strategic approach to threat management, ensuring the safety of your valuable data and systems.
 Jonathan Taylor Thomas Then & Now!
Jonathan Taylor Thomas Then & Now!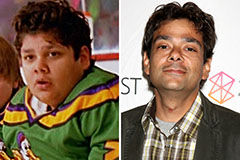 Shaun Weiss Then & Now!
Shaun Weiss Then & Now!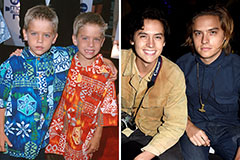 Dylan and Cole Sprouse Then & Now!
Dylan and Cole Sprouse Then & Now! Burke Ramsey Then & Now!
Burke Ramsey Then & Now! Naomi Grossman Then & Now!
Naomi Grossman Then & Now!